Introduction
Microsoft 365 security score is a consolidated security score based on Microsoft best practice security configurations for Microsoft 365 tenants. The higher the score the higher theoretically your overall Microsoft 365 tenant security levels. The score comprises a list of improvement actions based on your current security posture. Not all improvement actions may be appropriate for all tenants, since individual designs and security policies may dictate a different approach or configuration for some of the security improvement actions
Mandatory security considerations
Firstly, you need to ensure that you have a map of users and their roles in your Microsot 365 organization, including Global Admins and user, service and helpdesk administrators. Always apply the least privilege principle when granting permissions to users and administrators and minimize the number of global administrators to ideally two (2). All other administrators should utilize Microsoft 365 Privileged Access Management, assuming you fulfill the licensing requirements.
You may need to consider buying extra Premium P1 or P2 licenses for all or some of your users, to utilize additional security features, such as conditional access policies and Privileged Identity Management (PIM). Review the following article with a security feature comparison in the various Azure AD licensing plans: https://www.microsoft.com/en-us/security/business/identity-access/azure-active-directory-pricing.
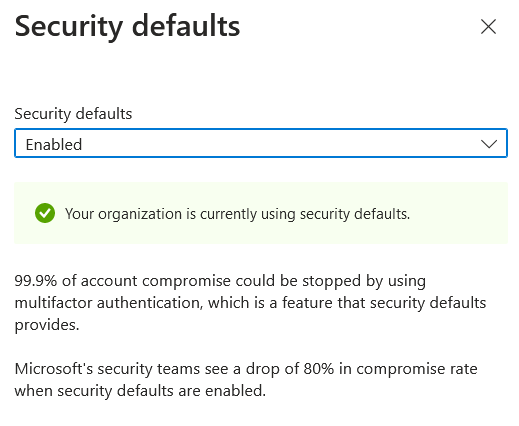
A mandatory action is to ensure that Azure AD security defaults are enabled. This can be done from the Azure AD portal, by navigating to the following location: https://aad.portal.azure.com/#view/Microsoft_AAD_IAM/ActiveDirectoryMenuBlade/~/Properties and click on "Manage Security Defaults" at the bottom of the Properties page.
Microsoft 365 secure score top 10 improvement actions
The following are the top 10 most important improvement actions in Microsoft Secure Score. Carrying out these improvement actions will get you the most points and significantly increase the Secure Score and your overall Microsoft 365 security posture.
- Require MFA for administrative roles. Requiring multi-factor authentication (MFA) for all administrative roles makes it harder for attackers to access accounts. Administrative roles have higher permissions than typical users. If any of those accounts are compromised, critical devices and data is open to attack. Ensure that you migrate from legacy MFA and SSPR policies and setup your modern authentication methods in Azure AD.
- Ensure all users can complete multi-factor authentication for secure access. Multi-factor authentication (MFA) helps protect devices and data that are accessible to these users. Adding more authentication methods, such as the Microsoft Authenticator app or a phone number, increases the level of protection if one factor is compromised.
- Enable policy to block legacy authentication. Today, most compromising sign-in attempts come from legacy authentication. Older office clients such as Office 2010 don’t support modern authentication and use legacy protocols such as IMAP, SMTP, and POP3. Legacy authentication does not support multi-factor authentication (MFA). Even if an MFA policy is configured in your environment, bad actors can bypass these enforcements through legacy protocols.
- Do not expire passwords. There is a long running debate on whether expiring passwords is a good or bad security practice. Research has found that when periodic password resets are enforced, passwords become less secure. Users tend to pick a weaker password and vary it slightly for each reset. If a user creates a strong password (long, complex and without any pragmatic words present) it should remain just as strong in the future as it is today. It is Microsoft's official security position to not expire passwords periodically without a specific reason, and recommends that cloud-only tenants set the password policy to never expire.
- Turn on sign-in risk policy. Turning on the sign-in risk policy ensures that suspicious sign-ins are challenged for multi-factor authentication (MFA).
- Turn on user risk policy. With the user risk policy turned on, Azure Active Directory detects the probability that a user account has been compromised. As an administrator, you can configure a user risk conditional access policy to automatically respond to a specific user risk level. For example, you can block access to your resources or require a password change to get a user account back into a clean state.
- Do not allow users to grant consent to unmanaged applications. Tighten the security of your services by regulating the access of third-party integrated apps. Only allow access to necessary apps that support robust security controls. Third-party applications are not created by Microsoft, so there is a possibility they could be used for malicious purposes like exfiltrating data from your tenancy. Attackers can maintain persistent access to your services through these integrated apps, without relying on compromised accounts.
- Configure which users are allowed to present in Teams meetings. Only allow users with presenter rights to share content during meetings. Restricting who can present limits meeting disruptions and reduces the risk of unwanted or inappropriate content being shared.
- Only invited users should be automatically admitted to Teams meetings. Users who aren’t invited to a meeting shouldn’t be let in automatically, because it increases the risk of data leaks, inappropriate content being shared, or malicious actors joining. If only invited users are automatically admitted, then users who weren’t invited will be sent to a meeting lobby. The host can then decide whether or not to let them in.
- Turn on customer lockbox feature. Turning on the customer lockbox feature requires that approval is obtained for datacenter operations that grants a Microsoft employee direct access to your content. Access may be needed by Microsoft support engineers if an issue arises. There's an expiration time on the request and content access is removed after the support engineer has fixed the issue.
- Ok this is the eleventh action but it is included here as it is regarded as important. It is related to enabling Self Service Password Reset (SSPR). With self-service password reset in Azure Active Directory, users no longer need to engage help desk to reset passwords. This feature works well with Azure AD dynamically banned passwords, which prevents easily guessable passwords from being used.
