Introduction to VPN and Zero Trust clients
VPN (Virtual Private Network) and Zero Trust are both approaches to network security, but they differ in their underlying principles and methods of securing network connections.
VPN (Virtual Private Network)
A VPN is a network technology that creates a secure and encrypted connection over a public network, such as the internet. It establishes a virtual tunnel between the user's device and the target network, allowing the user to access resources on the network as if they were directly connected to it. The main features of VPN are:
- Secure Communication: VPN encrypts the data transmitted between the user's device and the network, ensuring confidentiality and preventing unauthorized access.
- Remote Access: VPN enables users to access private network resources remotely, which is useful for remote workers or individuals accessing private networks from public Wi-Fi networks.
- IP Address Masking: VPN can mask the user's IP address, making it appear as if they are connecting from a different location, which enhances privacy and bypasses certain geo-restrictions.
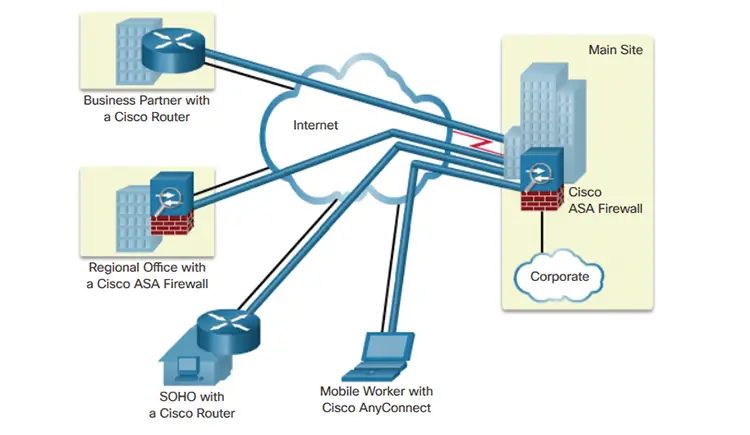
There are two types of VPN access, Point-to-Site (P2S) and Site-to-Site (S2S). A generic architecture for Site-to-Site VPN is shown below.
Zero Trust Network Access (ZTNA)
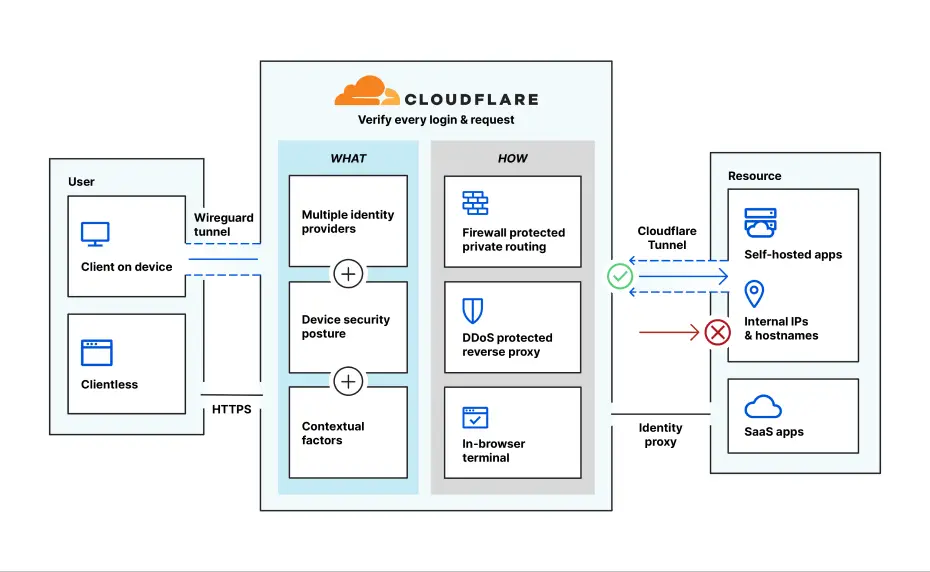
Zero Trust is an information security framework that assumes no trust for any user, device, or network component, regardless of their location. It emphasizes verifying and validating every access request, regardless of whether the request originates from inside or outside the network perimeter. The main principles of Zero Trust include:
- Identity-Based Access: Zero Trust focuses on verifying the identity of users and devices before granting access to network resources.
- Least Privilege: Zero Trust provides users with the minimum level of access required to perform their tasks, reducing the risk of unauthorized access to sensitive resources.
- Continuous Authentication: Zero Trust employs continuous monitoring and authentication to ensure ongoing trustworthiness of users and devices throughout their session.
A generic architecture of Zero Trust Network Access (ZTNA) is shown below.
Downloading VPN and Zero Trust clients
VPN Clients
The following list includes the most common and recognized VPN clients. Some VPN clients, such as Cisco AnyConnect and OpenVPN, assume that there is an on-premise or cloud managed VPN server to which the client would connect. Some other VPN clients assume a fully-hosted VPN server, such as in the case of NordVPN and ExpressVPN. This latter VPN client category is primarily used when you need a VPN proxy to enhance your privacy and anonymous Web browsing.
- Cisco AnyConnect:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: https://www.cisco.com/c/en/us/support/security/anyconnect-secure-mobility-client/tsd-products-support-series-home.html
- OpenVPN:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: https://openvpn.net/community-downloads/
- NordVPN:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: https://nordvpn.com/download/
- ExpressVPN:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL:
- CyberGhost VPN:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: https://www.cyberghostvpn.com/en_US/apps/windows-vpn
- PureVPN:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: https://www.purevpn.com/download
- Check Point Endpoint Security VPN:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Check Point sales or authorized resellers for download details.
- Fortinet FortiClient VPN:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: https://www.fortinet.com/support/product-downloads.html
- Juniper Pulse Secure:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Juniper sales or authorized resellers for download details.
- Palo Alto GlobalProtect:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Palo Alto Networks sales or authorized resellers for download details.
- SonicWall Global VPN Client:
- Supported Operating Systems: Windows
- Download URL: https://www.sonicwall.com/support/knowledge-base/global-vpn-client-gvc-downloads/170503477203858/
- OpenConnect VPN (OpenConnect-GUI):
- Supported Operating Systems: Windows, macOS, Linux
- Download URL: https://www.infradead.org/openconnect/gui.html
- Aviatrix VPN Client:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Aviatrix sales or authorized resellers for download details.
- WatchGuard Mobile VPN:
- Supported Operating Systems: Windows, macOS, iOS, Android
- Download URL: Contact WatchGuard sales or authorized resellers for download details.
- F5 BIG-IP Edge Client:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact F5 Networks sales or authorized resellers for download details.
Bear in mind that each operating system has its own native VPN client implementations, such as the VPN client in Windows and Linux operating systems.
Zero Trust (ZTNA) Clients
The following list includes the most common and recognized VPN clients.
- Zscaler Private Access:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Zscaler sales or authorized resellers for download details.
- Akamai Enterprise Application Access:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Akamai sales or authorized resellers for download details.
- Palo Alto Networks Prisma Access:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Palo Alto Networks sales or authorized resellers for download details.
- Cloudflare Access:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Cloudflare sales or authorized resellers for download details.
- Appgate SDP:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Appgate sales or authorized resellers for download details.
- Perimeter 81:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Perimeter 81 sales or authorized resellers for download details.
- Axis Security:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Axis Security sales or authorized resellers for download details.
- Netskope Private Access:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Netskope sales or authorized resellers for download details.
- Cato Networks ZTNA:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Cato Networks sales or authorized resellers for download details.
- CloudGenix AppFabric:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact CloudGenix sales or authorized resellers for download details.
- Citrix Secure Workspace Access:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Citrix sales or authorized resellers for download details.
- AppGate SDP (CyberArk):
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact CyberArk sales or authorized resellers for download details.
- Illumio Edge:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Illumio sales or authorized resellers for download details.
- PerimeterX:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact PerimeterX sales or authorized resellers for download details.
- Safe-T Software-Defined Perimeter:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Safe-T sales or authorized resellers for download details.
- F5 BIG-IP Access Policy Manager:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact F5 Networks sales or authorized resellers for download details.
- Juniper Secure Access SSL VPN:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Juniper sales or authorized resellers for download details.
- Cisco Duo Security:
- Supported Operating Systems: Windows, macOS, Linux, iOS, Android
- Download URL: Contact Cisco sales or authorized resellers for download details.
