Introduction
Microsoft has removed Basic authentication and the smtp auth option in Exchange Online services, i.e. Exchange Online for Exchange ActiveSync (EAS), POP, IMAP, Remote PowerShell, Exchange Web Services (EWS), Offline Address Book (OAB), Outlook for Windows, and Mac. The Microsoft Security defaults configuration and modern authentication are the successor technologies and use OAuth 2.0 token-based authorization.
Action items for end customers
There are various ways to tell if your applications are using basic authentication and not modern authentication to connect to Exchange Online. For Microsoft Outlook client, if you click CTRL and right-click the Outlook icon in the system tray, then click "Connection Status", the Authn column in the Outlook Connection Status dialog shows the value of Clear for basic authentication and the value of Bearer for modern authentication. You can also use the Azure AD sign-in report to determine which tenants and users are still using basic authentication.
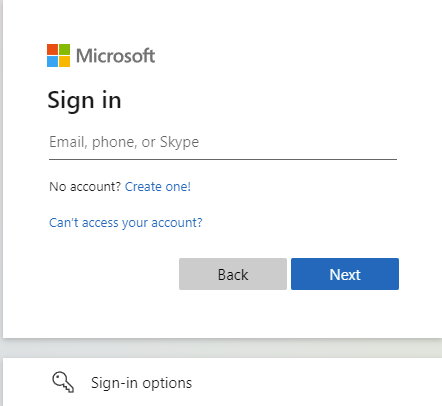
Modern authentication to Exchange Online presents a Web-based login screen such as the following.
Basic authentication on the other hand presents a Windows form similar to the following.

To enable or disable modern authentication for your M365 tenant, follow instructions in the article below: https://docs.microsoft.com/en-us/exchange/clients-and-mobile-in-exchange-online/enable-or-disable-modern-authentication-in-exchange-online
The following cases will be impacted by the replacement of basic authentication with modern authentication:
- Application developers who have built apps that send, read, or otherwise process email using these protocols will be able to keep the same protocol, but need to implement secure, modern authentication experiences for their users. Detailed guidance is provided at: https://docs.microsoft.com/en-us/exchange/client-developer/legacy-protocols/how-to-authenticate-an-imap-pop-smtp-application-by-using-oauth. Also if you are the developer of a custom application utilizing Exchange Web Services (EWS), you will need to switch to the Microsoft Graph API. Detailed instructions are provided at: https://techcommunity.microsoft.com/t5/exchange-team-blog/upcoming-changes-to-exchange-web-services-ews-api-for-office-365/ba-p/608055.
- Exchange Active Sync mobile device users will need to ensure that their mobile device email app is using modern authentication. One option is to use Outlook for iOS and Android when connecting to Exchange Online, because these apps natively support Modern authentication. There are other mobile device email apps which support Modern authentication. The built-in email apps for all popular platforms typically support Modern authentication, so you need to verify that your mobile device is running the latest version of the app. If the email app is current, but is still using Basic authentication, you might need to remove the account from the device and then add it back.
- If you are a Powershell administrator and need to run scripts against an Exchange Online tenant, you need to make use of the EXO V2 module which uses Modern authentication and works with multi-factor authentication (MFA) for connecting to all Exchange-related PowerShell environments in Microsoft 365: Exchange Online PowerShell, Security & Compliance PowerShell, and standalone Exchange Online Protection (EOP) PowerShell. The EXO V2 module can also be used non-interactively, which enables running unattended scripts via certificate-based authentication. certificate-based authentication for Powershell unattended scripts is described at App-only authentication for unattended scripts in the EXO V2 module.
- Regarding Microsoft Outlook client support for modern authentication you should consult the following articles: https://docs.microsoft.com/en-us/office365/enterprise/modern-auth-for-office-2013-and-2016 and New minimum Outlook for Windows version requirements for Microsoft 365. All versions of Outlook for Windows since 2016 have Modern authentication enabled by default, so it's likely that you're already using Modern authentication. Outlook Anywhere (formerly known as RPC over HTTP) has been deprecated in Exchange Online in favor of MAPI over HTTP. Outlook for Windows uses MAPI over HTTP, EWS, and OAB to access mail, set free/busy and out of office, and download the Offline Address Book. All of these protocols support Modern authentication. Outlook 2007 or Outlook 2010 cannot use Modern authentication, and will eventually be unable to connect. Outlook 2013 requires a setting to enable Modern authentication, but once you configure the setting, Outlook 2013 can use Modern authentication with no issues. Outlook 2013 requires a minimum update level to connect to Exchange Online. Outlook for Mac supports modern authentication.
- If you have public folders in a legacy Exchange server-based system, you will need to consult the following article to migrate to Exchange Online with modern authentication support: https://techcommunity.microsoft.com/t5/exchange-team-blog/announcing-public-folder-migration-scripts-with-modern/ba-p/3382800.
