Case #
You need to enable Just In Time JIT access for an Azure VM. A just-in-time access enables you to lock down inbound traffic to your VM by allowing access for only a limited time. The just-in-time feature is available as part of the Microsoft Defender for Cloud standard tier. Azure Security Center and Azure Defender are now called Microsoft Defender for Cloud. The goal of JIT is to ensure that even though your inbound traffic is locked down, Defender for Cloud still provides easy access to connect to VMs when needed. You can request access to a JIT-enabled VM from Defender for Cloud, Azure virtual machines, PowerShell, or the REST API.
More details on how Azure VM JIT works can be found in the following article: https://docs.microsoft.com/en-us/azure/defender-for-cloud/just-in-time-access-overview.
Solution #
Follow the procedure below to enable Azure VM JIT. You may need to upgrade your Security Center subscription to enable a just-in-time access. A 30-day trial of Microsoft Defender for Cloud standard is usually available in most Azure subscriptions.
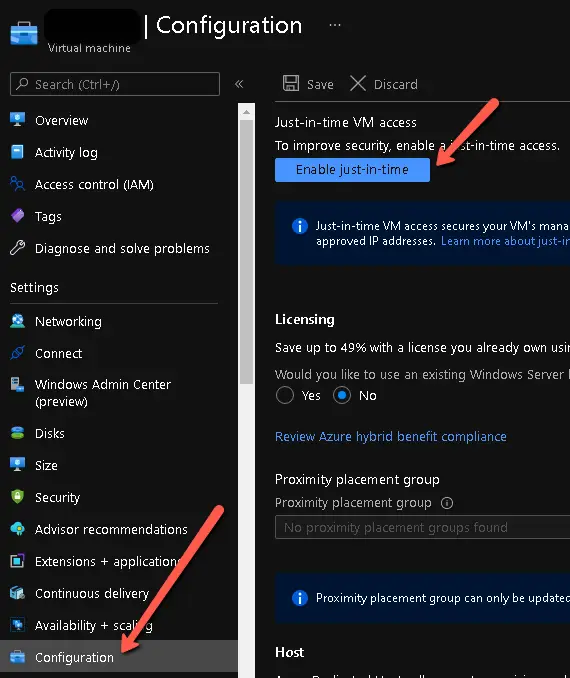
- Navigate to your Azure VM resource and open the "Configuration" pane. Click on "Enable just-in-time" button.
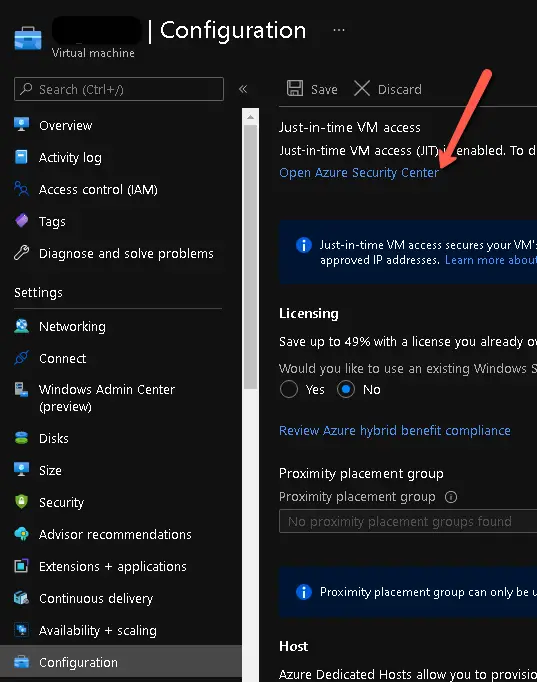
- After JIT is enabled, on the same "configuration" pane of your Azure VM, click on "Open Azure Security Center" to configure JIT for your VM.
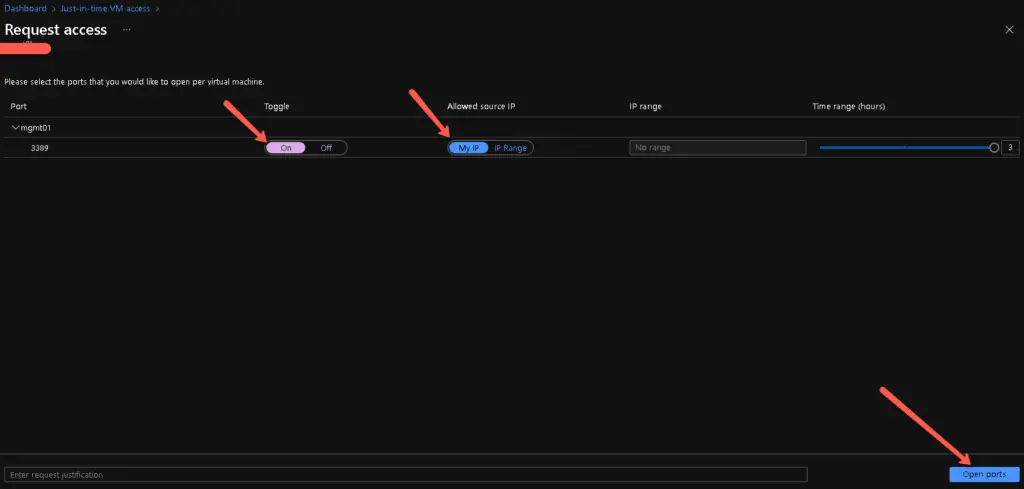
- In the Microsoft Defender for Cloud (former Azure Security Center) portal, you tick your VM and click on "Request Access".
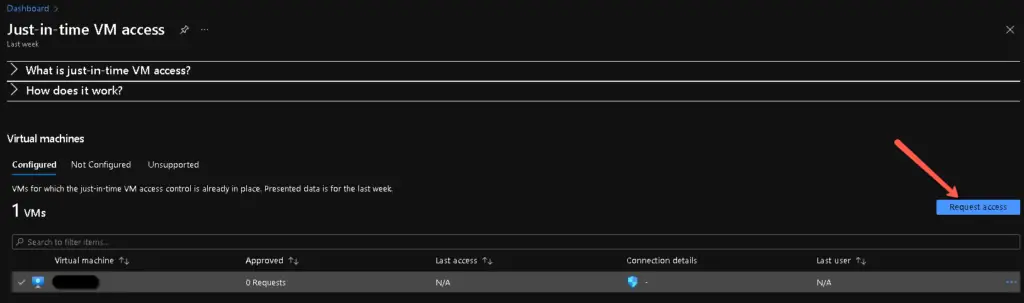
Afterwards choose the RDP port, enable access for a maximum amount of time required and click "Open Ports".
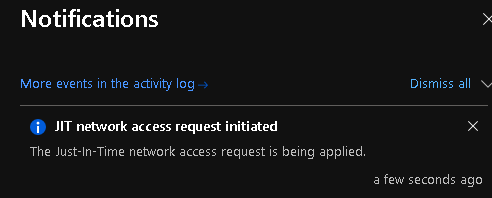
You will afterwards receive a notification that the requested JIT access is being applied (using NSG/Firewall rules in the backend).
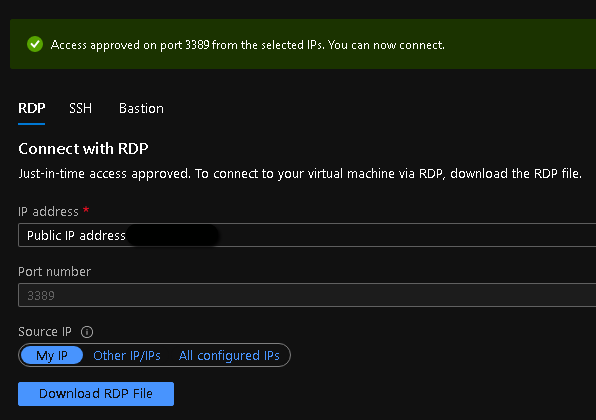
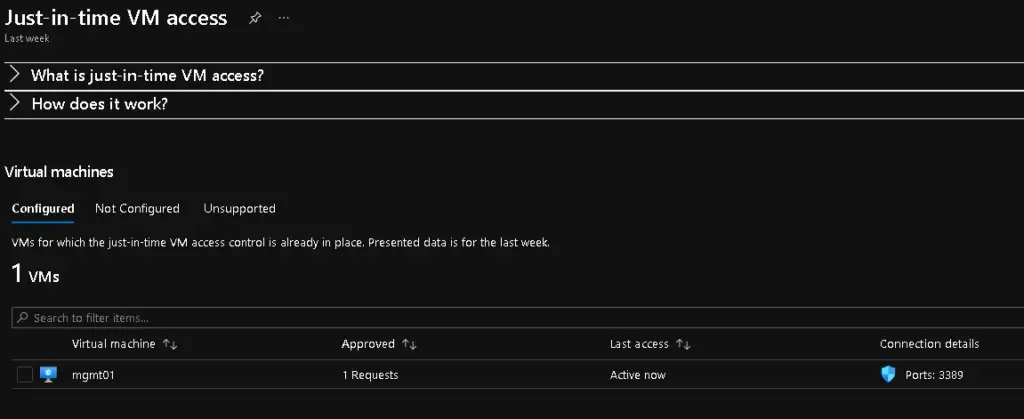
The status of the JIT access should now be as shown in the screenshot below.
You can go ahead and access your VM with JIT enabled. From your Azure VM, go to the "Connect" pane, choose RDP and click on "Request access" again. After JIT access has been granted, click on "Download RDP file".