Case #
You need to configure a Windows Server Update Services (WSUS) server to provide Windows updates to all servers in your on-premises infrastructure. There are various WSUS architecture options for high availability, however this article will focus on the simple scenario of how to configure a WSUS standalone server, which can cover the requirements of many infrastructures.
Solution #
WSUS installation and configuration #
Carry out the steps below to install and configure a WSUS standalone server.
- Setup the VM or physical machine where the WSUS server role will be installed, join the machine to your AD domain and install all latest Windows updates and third party application patches.
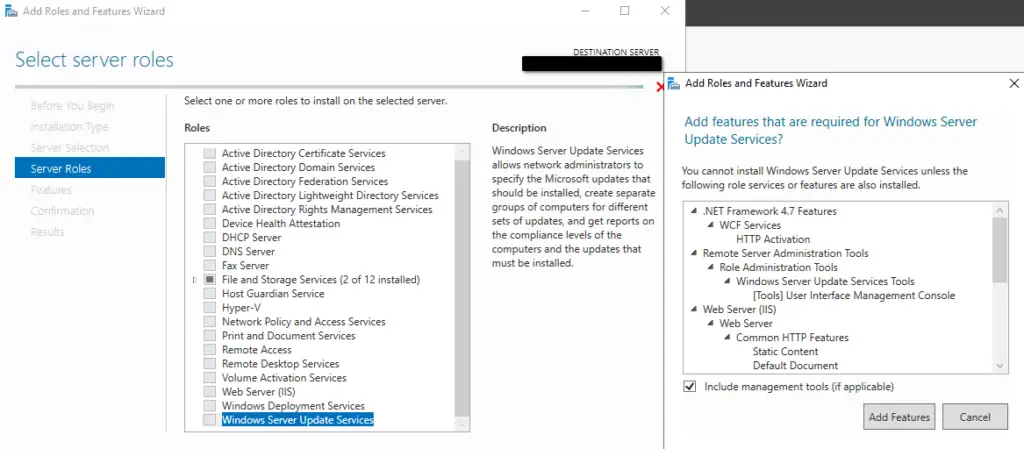
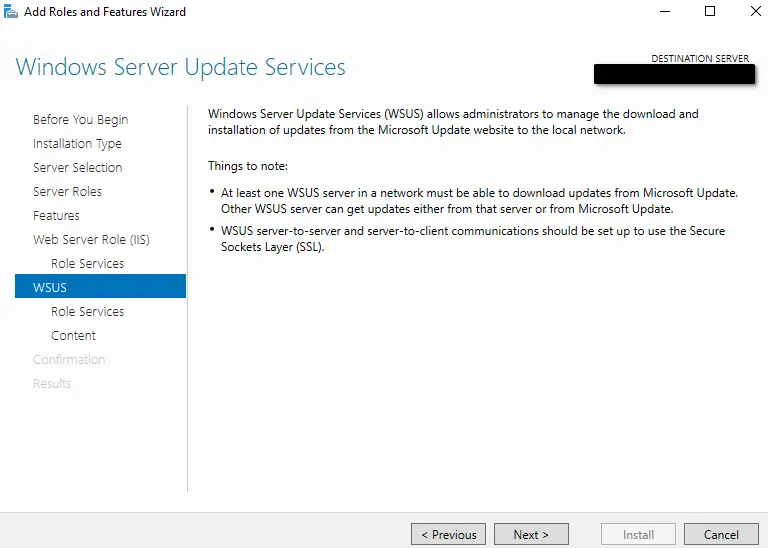
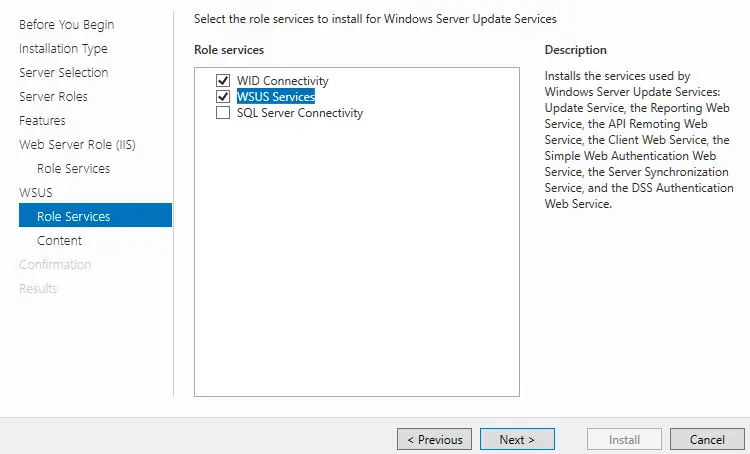
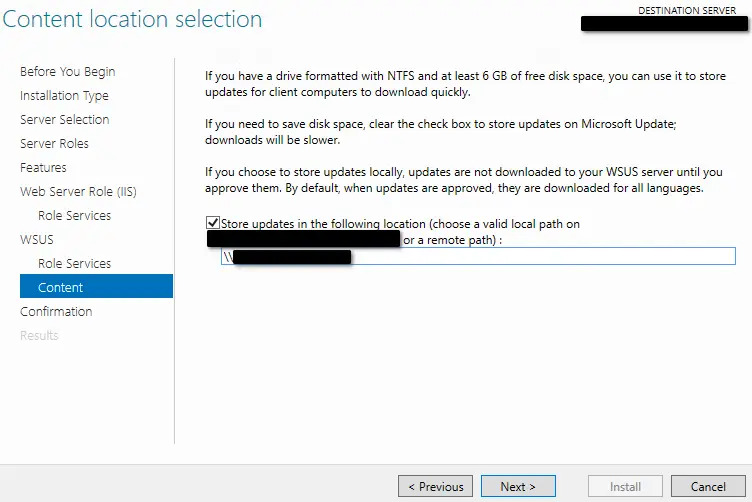
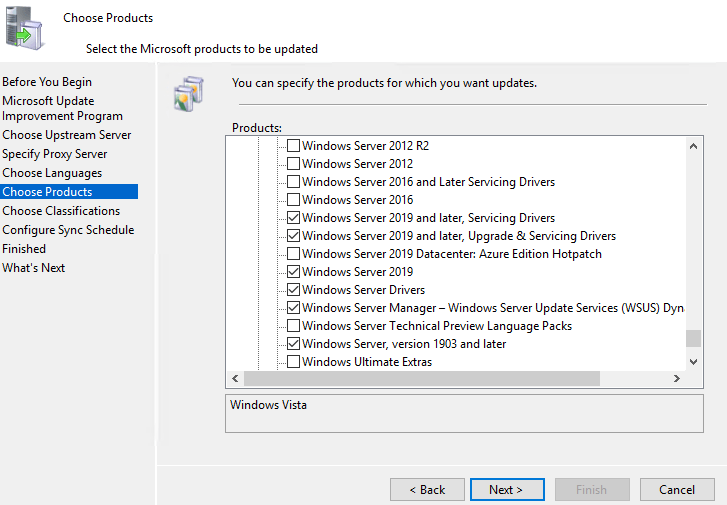
- Install the WSUS server role in the Windows Server Manager with Windows Internal Database (WID), setup the required UNC path for WSUS storage with proper SMB and NTFS permissions, as per https://stefanos.cloud/kb/windows-server-update-services-wsus-share-permissions/. Allow for minimum of 500 GB for this file share. The total required disk space is dependent on your choice of Windows Update types, as explained later in this post.
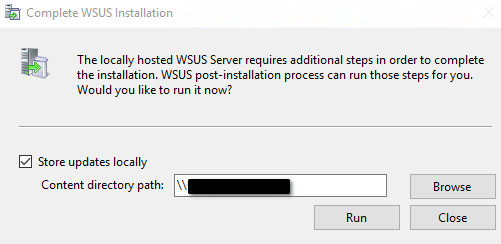
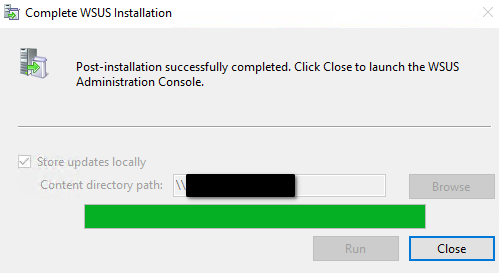
- After rebooting the server, run the WSUS post-installation process when you launch the WSUS MMC console. Click Run to continue.
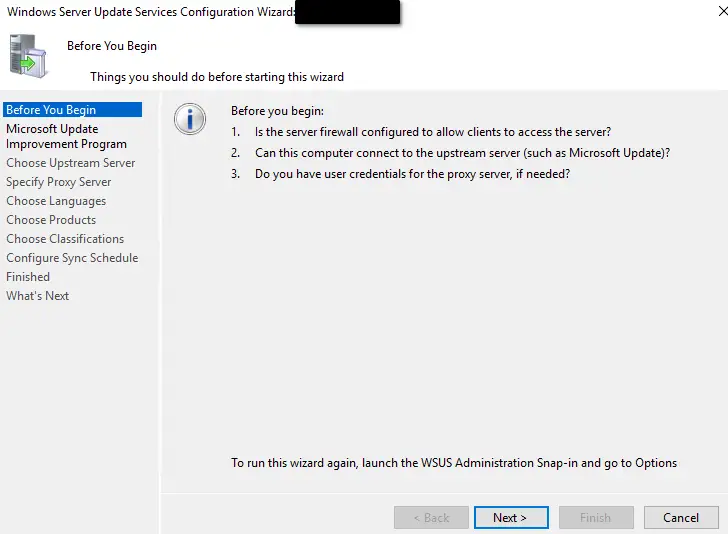
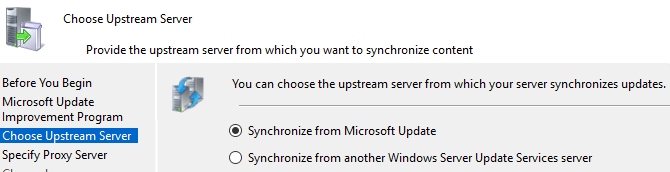
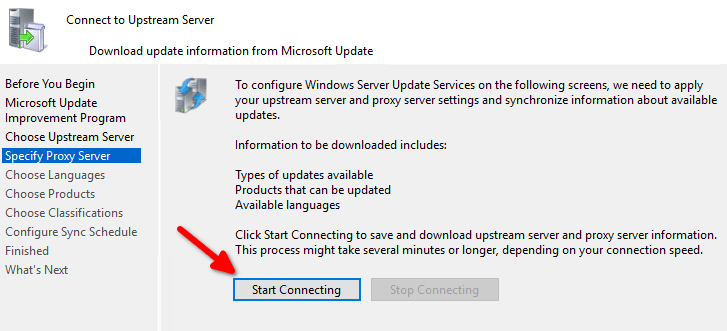
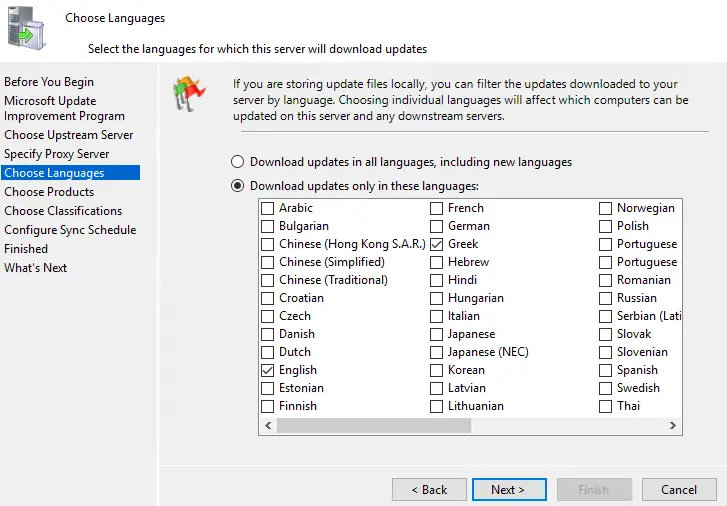
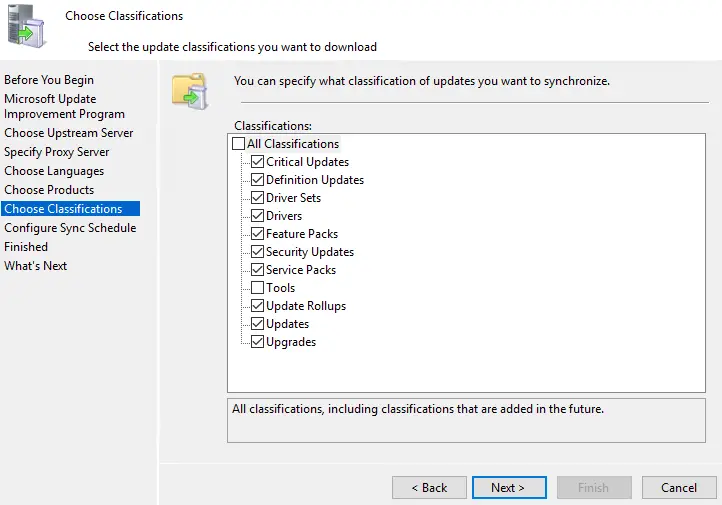
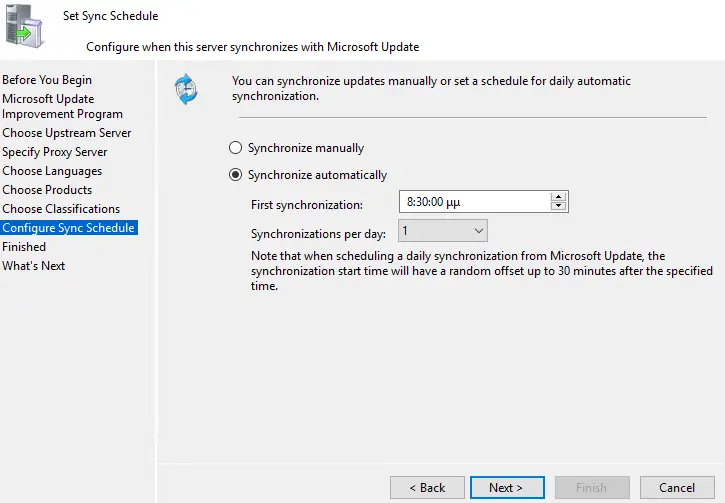
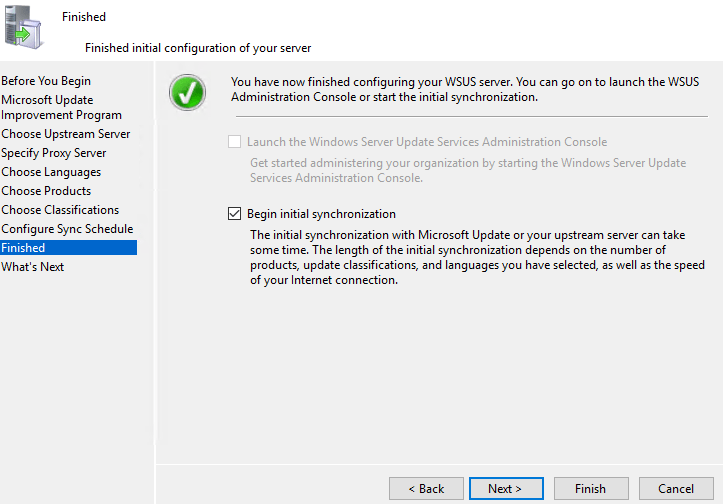
- Run the WSUS first time configuration wizard in Microsoft Management Console (MMC) for the initial synchronization, setup proxy and synchronization schedule and configure SSL for WSUS if needed, as per the following instructions: https://docs.microsoft.com/en-us/windows-server/administration/windows-server-update-services/deploy/2-configure-wsus.
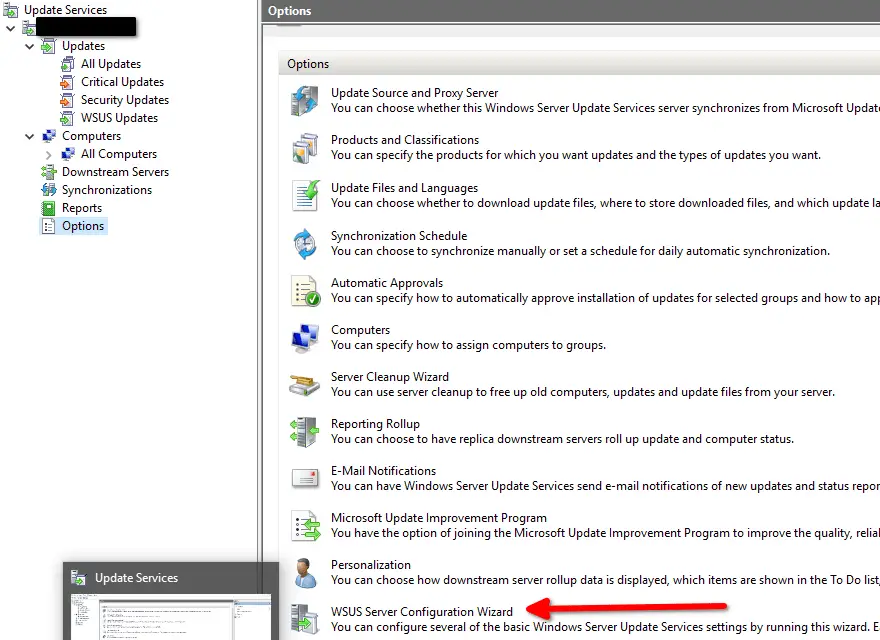
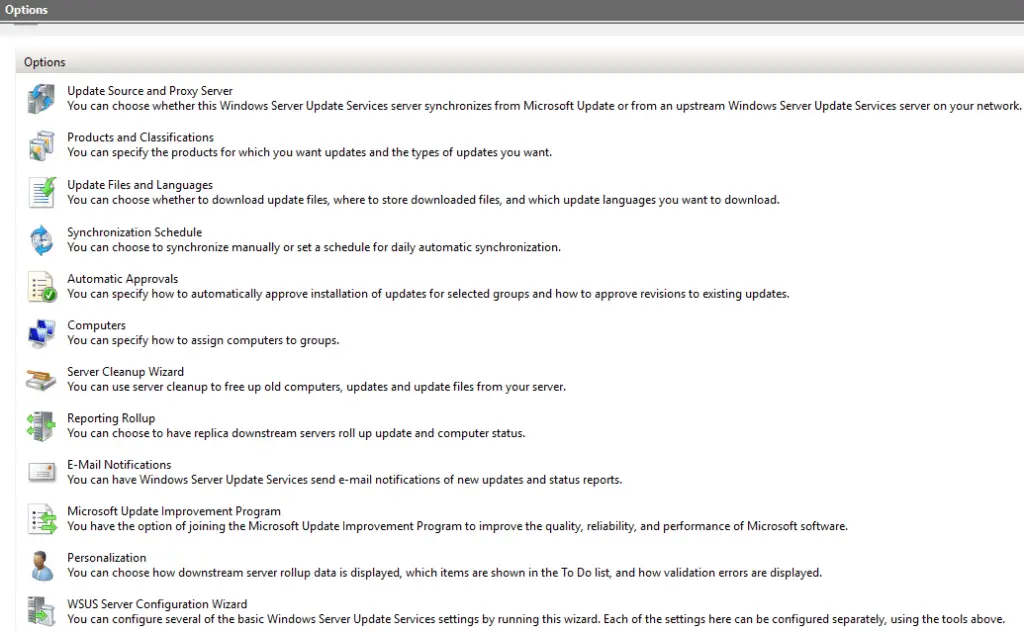
- Configure all other WSUS options in the above "Options" pane, as per your environment requirements.
- Configure WSUS SSL as per: https://docs.microsoft.com/en-us/previous-versions/orphan-topics/ws.11/dn343567(v=ws.11)?redirectedfrom=MSDN.
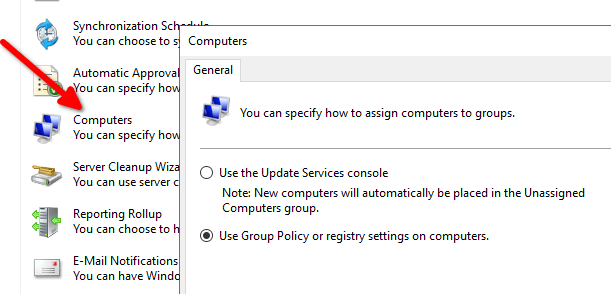
- Create computer groups, to organize WSUS targets in a logical fashion. Assign computers to groups for WSUS using GPO (client-side targeting) or manually by moving each computer object to the proper WSUS group inside the WSUS console (server-side targeting). You can define whether server-side targeting or client-side targeting will be used by clicking on the Computer section of WSUS options as shown in the screenshot.
- Configure WSUS auto-approval rules and Windows updates auto-install schedule via GPO policies as per the following instructions: https://docs.microsoft.com/en-us/windows-server/administration/windows-server-update-services/deploy/4-configure-group-policy-settings-for-automatic-updates.
- Approve and Deploy Updates in WSUS as per: https://docs.microsoft.com/en-us/windows-server/administration/windows-server-update-services/deploy/3-approve-and-deploy-updates-in-wsus.
A good practice for approvals and declinations is the following:
- Always enable the default WSUS approval rule which automatically approves all critical and security updates.
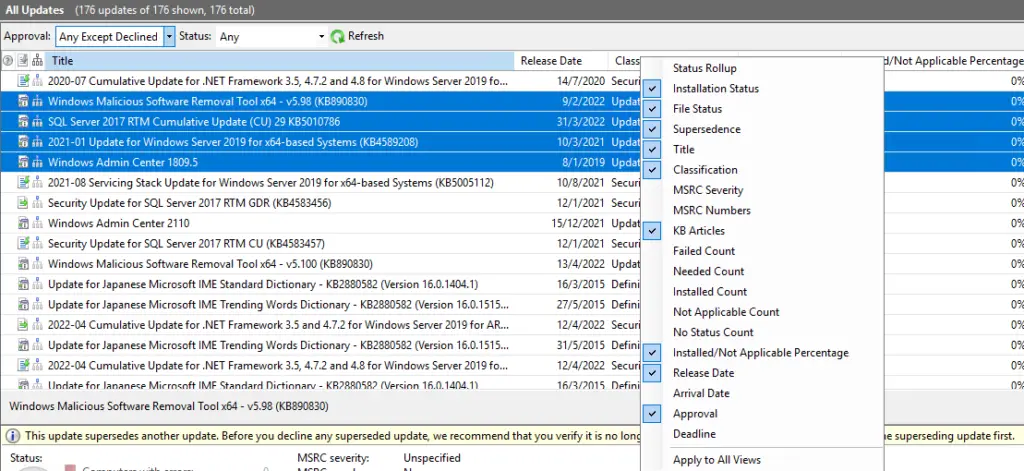
- Add extra columns for "Supersedence" in the "All Updates" section of the WSUS mmc console and review/approve all updates which supersede other updates.
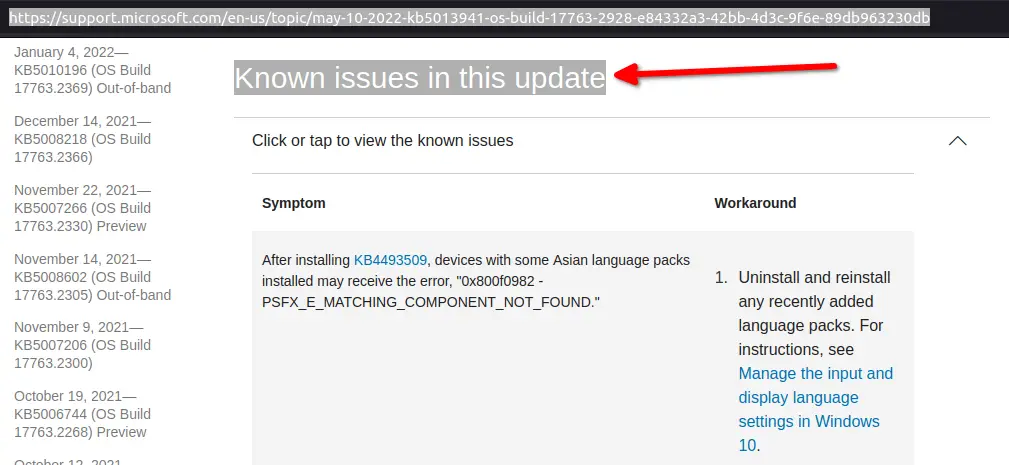
- Ensure that you review the "Known issues in this update" section of each new update which is included in your WSUS server update(s) notification emails, before deciding to approve each update.
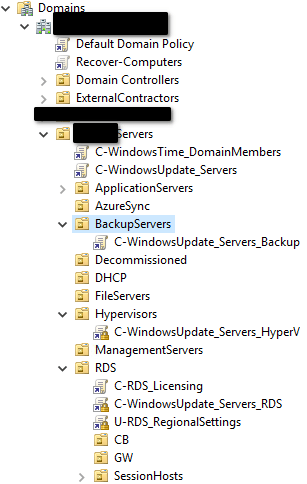
When organizing your on-premises Windows servers and workstations for WSUS automatic updates, it is a good practice to design your OU structure in such a way that you apply specific GPO to each group of servers (organized by server role) and each group of workstations (organized per department or other company policy grouping). One good option is to have a general (top-level) GPO for all your servers and then enforce additional WSUS objects per server role, for example one dedicated GPO for hypervisor hosts and one dedicated GPO for your RDS or Citrix servers.
The following examples shows such an OU design with WSUS GPO objects.
WSUS troubleshooting #
If you encounter any issues in your WSUS environment during initial testing, consult the following articles for WSUS troubleshooting:
- https://stefanos.cloud/kb/how-to-resolve-wsus-and-windows-update-common-errors/
- https://stefanos.cloud/kb/how-to-resolve-wsus-connection-error/
- https://docs.microsoft.com/en-us/troubleshoot/mem/configmgr/troubleshoot-issues-with-wsus-client-agents
- https://docs.microsoft.com/en-us/troubleshoot/mem/configmgr/troubleshoot-wsus-connection-failures
- https://docs.microsoft.com/en-us/troubleshoot/mem/configmgr/troubleshoot-wsus-import-sync-issues
- https://docs.microsoft.com/en-us/windows-server/administration/windows-server-update-services/manage/wsus-messages-and-troubleshooting-tips
- https://docs.microsoft.com/de-de/security-updates/windowsupdateservices/21669506
- https://docs.microsoft.com/en-us/troubleshoot/mem/configmgr/wsus-maintenance-guide
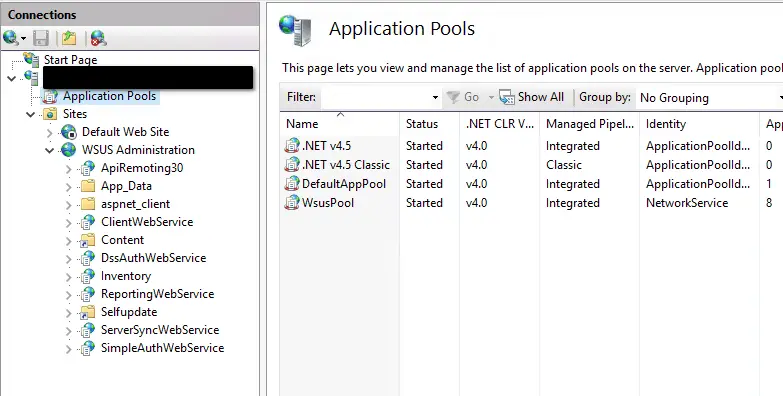
Also remember to check the following dependent components of the WSUS installation when performing troubleshooting:
- IIS manager and related files
- WSUS WID or SQL Server database
- Registry keys related to WSUS
- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate
- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU
- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate
- File share of the WSUS server and local Windows update cache on each WSUS target
To optimize performance and troubleshoot the WSUS components, refer to the following KB article:
WSUS server and updates monitoring #
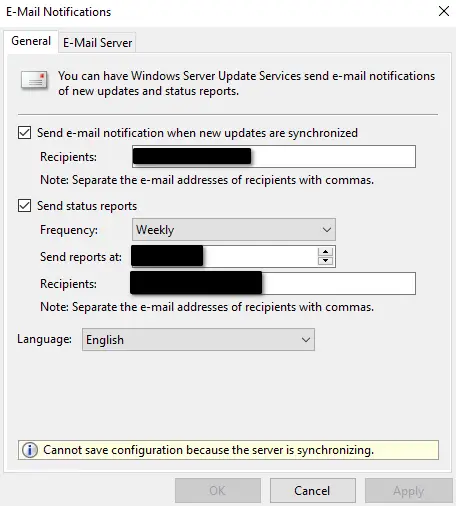
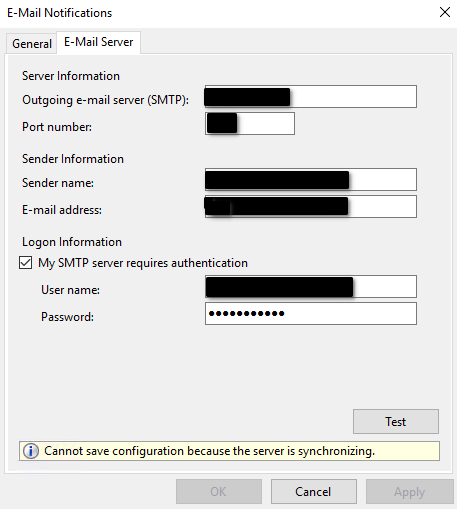
For monitoring the WSUS server, you should be using the MMC console and you should also remember to setup email alerts in order to proactively monitor the WSUS updates sync and any errors encountered.