Case #
You encounter errors when you try to login to Microsoft 365 services from your Windows 10 device. You may come across Azure AD device registration or join issues in an already existing device which is registered or joined to Azure AD.
Solution #
Understanding Azure AD device registration and join #
First off, you need to understand the basic concepts behind Azure AD device registration and join.
A device identity is an object in Azure Active Directory (Azure AD). This device object is similar to users, groups, or applications. A device identity gives administrators information they can use when making access or configuration decisions. There are three ways to get a device identity:
Device identities are a prerequisite for scenarios like device-based Conditional Access policies and Mobile Device Management with Microsoft Endpoint Manager.
Also you need to have an understanding of which operating systems and devices can be registered or joined to Azure AD. The following comparison matrix shows all supported operating systems and features per Azure AD registration/join option. Apple iOS, MacOS and Android operating systems are also supported for Azure AD registration. More details on the operating system supported versions can be found at: https://docs.microsoft.com/en-us/mem/intune/fundamentals/supported-devices-browsers.
| Consideration | Azure AD registered | Azure AD joined | Hybrid Azure AD joined |
|---|---|---|---|
| Client operating systems | |||
| Windows 10 devices |  |  |  |
| Windows down-level devices (Windows 8.1 or Windows 7) |  | ||
| Sign in options | |||
| End-user local credentials |  | ||
| Password |  |  |  |
| Device PIN |  | ||
| Windows Hello |  | ||
| Windows Hello for Business |  |  | |
| FIDO 2.0 security keys |  |  | |
| Microsoft Authenticator App (passwordless) |  |  |  |
| Key capabilities | |||
| SSO to cloud resources |  |  |  |
| SSO to on-premises resources |  |  | |
| Conditional Access (Require devices be marked as compliant) (Must be managed by MDM) |  |  |  |
| Conditional Access (Require hybrid Azure AD joined devices) |  | ||
| Self-service password reset from the Windows login screen |  |  | |
| Windows Hello PIN reset |  |  |
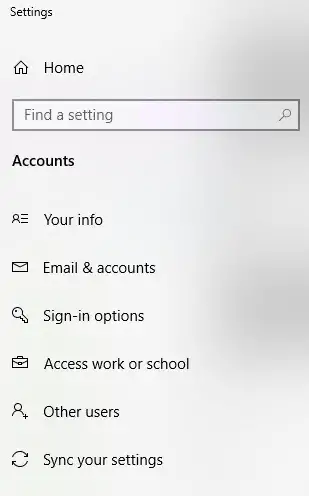
Windows account options #
Windows 10 and Windows 11 can be installed with the following installation user options:
- Local user (offline)
- Microsoft Account (MSA), which is a personal account using for example the outlook.com or hotmail.com UPNs.
- Microsoft work or school account, which is a Microsoft 365 account with Azure AD connectivity.
If you originally setup your system with a local account or MSA account, the information section will be linked to this account. Any Microsoft 365 available features which work with Azure AD require configuration of a M365 account in the "Work or School account" section.
Azure AD registration issues #
If you have Azure AD registration issues, you need to collect traces from the following items to troubleshoot further:
- Run the dsregcmd /verbose /status command. This will reveal useful information about all sync parameters of your device.
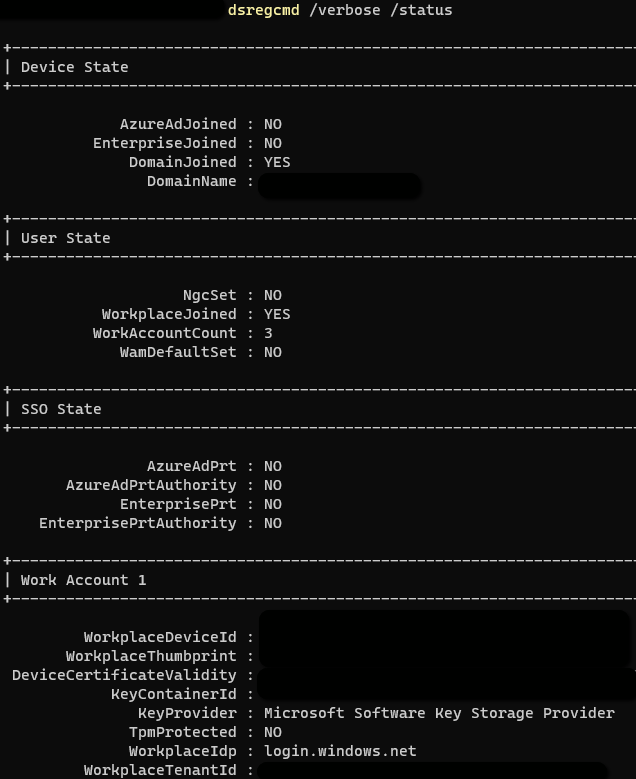
- After getting the device ID from the above command, check this device ID in the Microsoft 365 management portal at https://portal.azure.com/#blade/Microsoft_AAD_Devices/DevicesMenuBlade/Devices. Also compare this information with the Devices tab under your Microsoft 365 user account at: https://myaccount.microsoft.com.
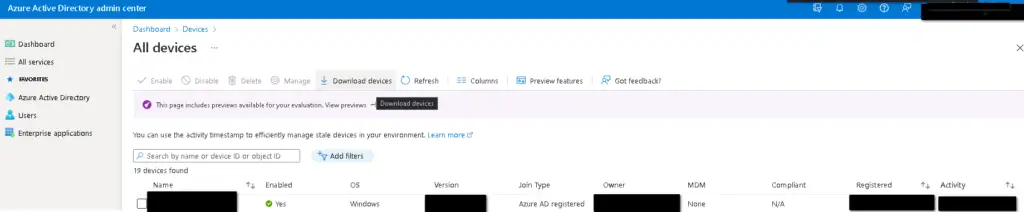
- To re-register a device, you can delete the device entry in Azure AD --> Devices section in the Azure AD management portal and disconnect the device from the "Windows 10/11 System Settings --> Accounts" section. Refer to the following article for a step-by-step process of re-registering or re-joining a device in Azure AD: https://docs.microsoft.com/en-us/azure/active-directory/devices/faq.
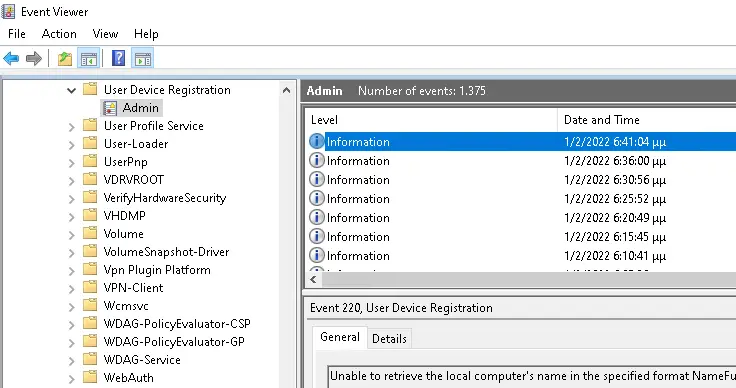
- Check the relevant event logs under Applications and Services logs --> Microsoft --> Windows --> User Device Registration.
- Remove all other Microsoft work accounts from your local machine and try connecting only with the account in question from Windows 10.
- Check the Office 365 apps activation status on the machine. If needed, run the Support and Recovery Assistant (SARA) tool from Microsoft.
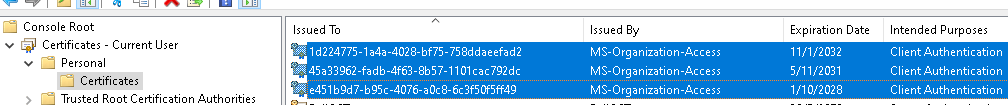
Check the validity and expiration date of the system-generated self-signed certs which are used for Azure AD registration and domain join. These TLS certs can be found under the user certificate store and have a name which is a GUID and are issued by "MSOrganization-Access", as shown in the example below.
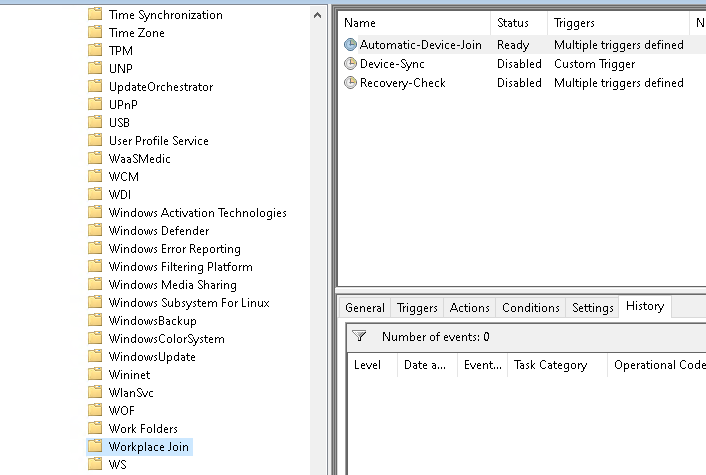
Check the scheduled task under path "Task Scheduler Library --> Microsoft --> Windows --> Workplace Join".
- Check the registry for Azure AD sync related entries.
- Receive Azure AD registration/join authentication traces and network traces by following steps below.
- For regular traces, download the following tool: https://aka.ms/icesdptool.
- For network traces, run the following steps.
Run netsh trace start scenario=internetClient_dbg capture=yes persistent=yes.
Lock and unlock the device. For hybrid-joined devices, wait a minute or more to allow the PRT acquisition task to finish.
Run netsh trace stop.
Azure AD join and hybrid AD join issues #
For hybrid AD join to work properly, check the following pre-requisites and troubleshooting steps. Remember that in hybrid Azure AD join cases, the on-premises Azure AD Connect tool's configuration is involved.
- https://docs.microsoft.com/en-us/azure/active-directory/hybrid/how-to-connect-sso-quick-start
- https://docs.microsoft.com/en-us/azure/active-directory/devices/hybrid-azuread-join-managed-domains
- https://neroblanco.co.uk/2021/02/troubleshooting-hybrid-ad-join/
Sources #
https://docs.microsoft.com/en-us/azure/active-directory/devices/overview
https://docs.microsoft.com/en-us/azure/active-directory/devices/concept-azure-ad-register
https://docs.microsoft.com/en-us/azure/active-directory/devices/concept-azure-ad-join
https://docs.microsoft.com/en-us/azure/active-directory/devices/concept-azure-ad-join-hybrid
https://docs.microsoft.com/en-us/azure/active-directory/devices/plan-device-deployment
https://docs.microsoft.com/en-us/azure/active-directory/devices/troubleshoot-device-dsregcmd
https://portal.azure.com/#blade/Microsoft_AAD_Devices/DevicesMenuBlade/Devices
https://docs.microsoft.com/en-us/azure/active-directory/devices/concept-azure-ad-register
https://docs.microsoft.com/en-us/azure/active-directory/devices/manage-stale-devices
https://docs.microsoft.com/en-us/azure/active-directory/devices/faq
https://docs.microsoft.com/en-us/azure/active-directory/devices/device-management-azure-portal



