Case #
You need to be able to monitor the global status of software and hardware security vulnerabilities and receive alerts when such vulnerabilities are released, based on filtering criteria. This should be part of your security and privacy strategy. This KB article provides guidance on how to setup monitoring and alerting for security vulnerabilities.
Solution #
There are various security vulnerability databases (SVD) out there, which organize and disseminate information about security vulnerabilities of hardware, firmware and software from any vendor, product or service. You should register for free with the most prominent SVDs and setup alerts to stay tuned about the most critical released Common Vulnerabilities and Exposures (CVEs). There are generic SVD databases with CVEs as well as vendor-specific SVD services. This article presents the most prominent services. This is not an exhaustive list but is a pretty useful one.
- Mitre.org is a global CVE database available at https://cve.mitre.org/index.html and on the new website at https://www.cve.org/. Both websites are active and should be used for different types of CVE searches. When running a CVE search based on CVE ID, use the latter site, while when running a CVE search based on keywords, use the former site. The CVE project is also being actively developed on Github at https://github.com/CVEProject. You can find more CVE search tips at https://cve.mitre.org/find/search_tips.html. N
- NIST National Vulnerability Database available at https://nvd.nist.gov/. According to NIST, a vulnerability is defined as a weakness in the computational logic (e.g., code) found in software and hardware components that, when exploited, results in a negative impact to confidentiality, integrity, or availability. Mitigation of the vulnerabilities in this context typically involves coding changes, but could also include specification changes or even specification deprecations (e.g., removal of affected protocols or functionality in their entirety).
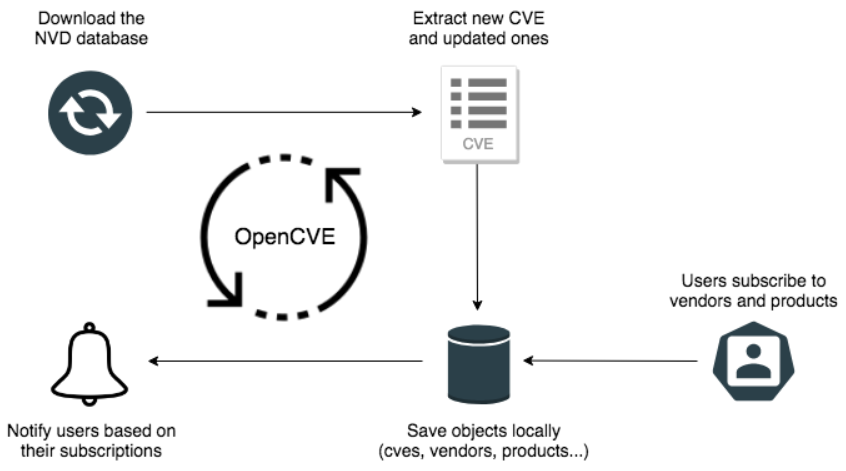
- OpenCVE is a platform used to locally import the list of CVEs and perform searches on it (by vendors, products, CVSS, CWE.). Users subscribe to vendors or products, and OpenCVE alerts them when a new CVE is created or when an update is done in an existing CVE. Many CVE are released every day, but you're not interested by all of them. OpenCVE allows you to filter the list by subscribing to vendors and their products. You can manually install OpenCVE, or use docker. OpenCVE also provide a running instance on https://www.opencve.io if you don't want to host it yourself.
You should register with OpenCVE.io to start receiving personalized alerts to your monitoring mailbox.
- Microsoft Defender Vulnerability Management reduces cyber risks with continuous vulnerability discovery and assessment, risk-based prioritization, and remediation of Microsoft products and services.
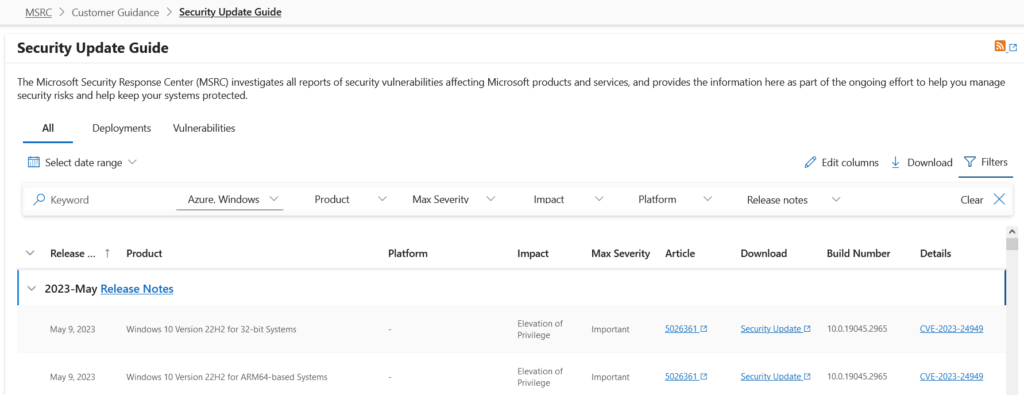
- Microsoft Security Response Center (MSRC). You should follow the steps described in Security Update Guide Notification System News: Create your profile now – Microsoft Security Response Center to subscribe to Security Notifications directly from the Security Update Guide (SUG). You will need to create a profile, and then select the notifications you want to receive via email. The Microsoft Security Response Center (MSRC) investigates all reports of security vulnerabilities affecting Microsoft products and services, and provides the information on the Security Update Guide as part of the ongoing effort to help you manage security risks and help keep your systems protected. An example is shown below.
- CVEDetails.com is another CVE database worth mentioning.
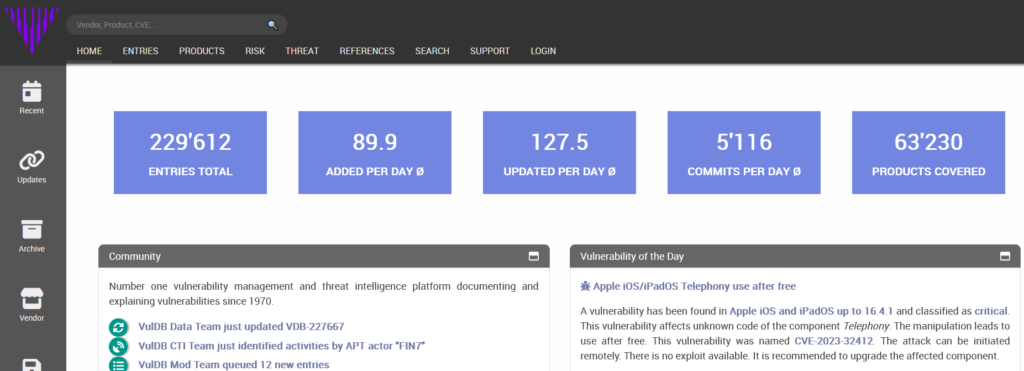
- Vuldb.com is a notenorthy service which offers alerting features to its registered users.
- Variotdbs.pl is a frontend for a database covering vulnerabilities and exploits related to Internet of Things (IoT) devices, constantly updated by harvesting various sources of information



